Papers
Unlocking the Path Towards Intelligent Telecom Marketplaces for Beyond 5G and 6G Networks
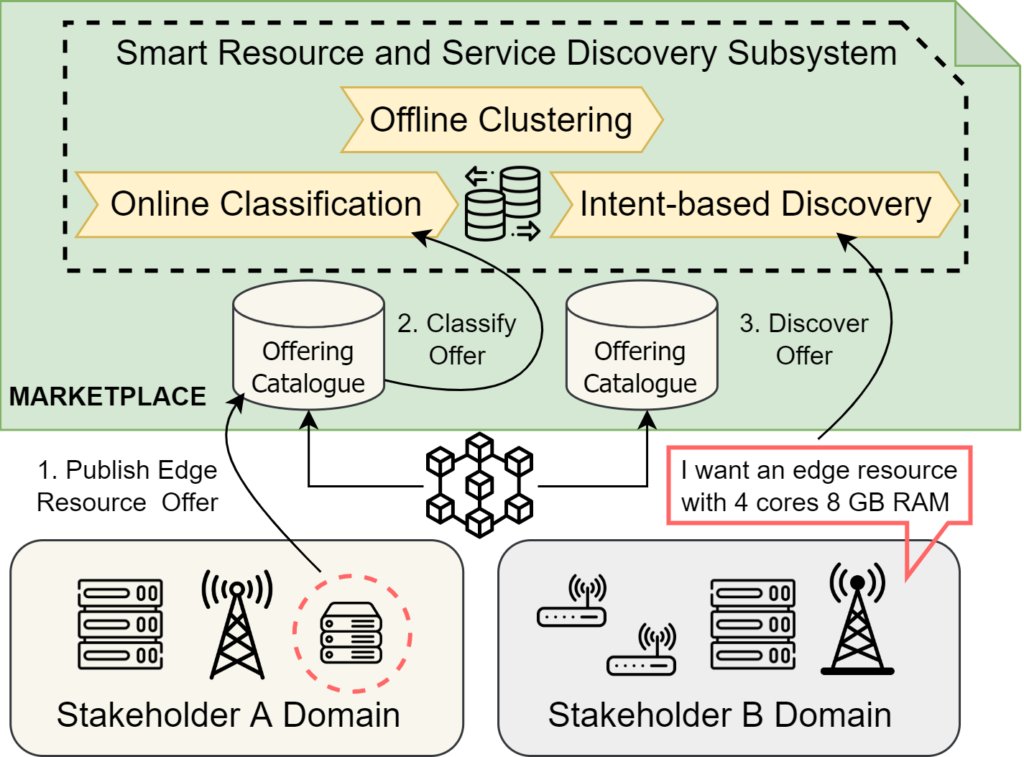
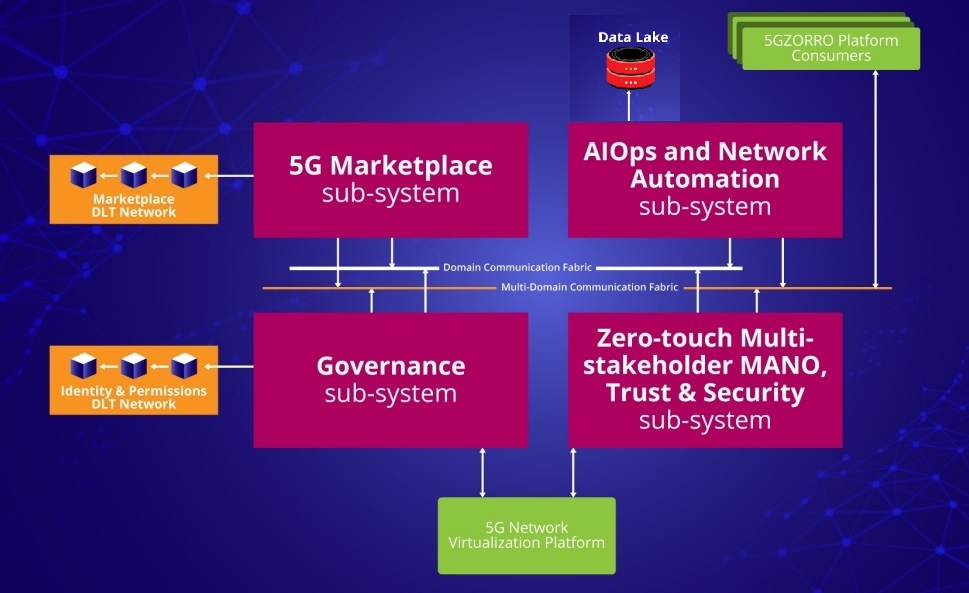
- Abstract: 6G systems are perceived to be heavily softwarised, and therefore, the collaboration among all stakeholders, such as network and cloud providers, operators, application developers, service providers and device and equipment vendors, shall occur via software in a secured, distributed, and automated manner. This could be envisioned with a broker less and immutable Marketplace anchored in Distributed Ledger Technologies, removing the need for a trusted party as Marketplace operator while avoiding this single point of failure, increasing transparency and flexibility of operational rules, and featuring automated contract negotiation and fulfilment supporting governance, delivery, and billing operations. This work goes a step forward and introduces a Smart Resource and Service Discovery application, based on intent recognition and Machine Learning assisted techniques, to enable the automated discovery of resources and services exposed over the Marketplace. Evaluation results demonstrate the accuracy of our approach and its suitability to provide decentralized Telecom Marketplaces with intelligent and data driven discovery capabilities.
- Related Info: paper can be read here
Authors: Adriana Fernandez-Fernandez, Estefania Coronado, Shuaib Siddiqui – i2CAT; Alberto Erspamer, Georgios Samaras, Vasileios Theodorou – INTRACOM Telecom
Zero Touch Management: A Survey of Network Automation Solutions for 5G and 6G Networks
Abstract: Mobile networks are facing an unprecedented demand for high-speed connectivity originating from novel mobile applications and services and, in general, from the adoption curve of mobile devices. However, coping with the service requirements imposed by current and future applications and services is very difficult since mobile networks are becoming progressively more heterogeneous and more complex. In this context, a promising approach is the adoption of novel network automation solutions and, in particular, of zero-touch management techniques. In this work, we refer to zero-touch management as a fully autonomous network management solution with human oversight. This survey sits at the crossroad between zero-touch management and mobile and wireless network research, effectively bridging a gap in terms of literature review between the two domains. In this paper, we first provide a taxonomy of network management solutions. We then discuss the relevant state-of-the-art on autonomous mobile networks. The concept of zero-touch management and the associated standardization efforts are then introduced. The survey continues with a review of the most important technological enablers for zero-touch management. The network automation solutions from the RAN to the core network, including end-to end aspects such as security, are then surveyed. Finally, we close this article with the current challenges and research directions.
- Related Info: paper can be read here
- Authors: Estefanía Coronado, Adriana Fernandez-Ferndez, Shuaib Siddiqui, Xavier Costa-Perez- i2CAT Foundation; Rasoul Behravesh – Fondazione Bruno Kessler
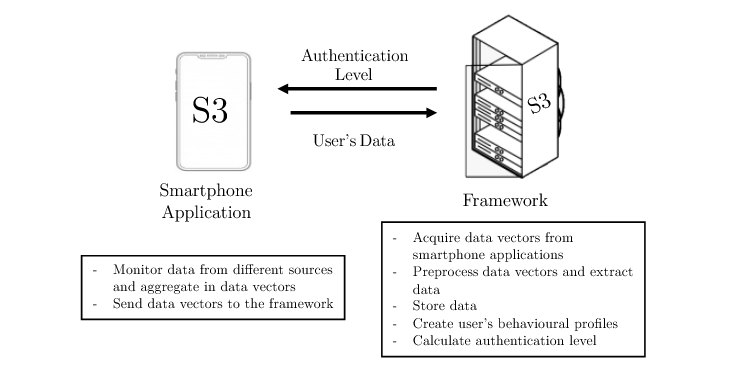
S3: An AI-Enabled User Continuous Authentication for Smartphones Based on Sensors, Statistics and Speaker Information
- Abstract: Continuous authentication systems have been proposed as a promising solution to authenticate users in smartphones in a non-intrusive way. However, current systems have important weaknesses related to the amount of data or time needed to build precise user profiles, together with high rates of false alerts. Voice is a powerful dimension for identifying subjects, but its suitability and importance have not been deeply analysed regarding its inclusion in continuous authentication systems. This work presents the S3 platform, an artificial intelligence-enabled continuous authentication system that combines data from sensors, applications statistics, and voice to authenticate users in smartphones. Experiments have tested the relevance of each kind of data, explored different strategies to combine them, and determined how many days of training are needed to obtain good enough profiles. Results showed that voice is much more relevant than sensors and applications statistics when building a precise authenticating system, and the combination of individual models was the best strategy. Finally, the S3 platform reached a good performance with only five days of use available for training the users’ profiles. As an additional contribution, a dataset with 21 volunteers interacting freely with their smartphones for more than sixty days has been created and made available to the community.
- Related Info: paper can be read here
- Authors: Juan Manuel Espín López, Javier G. Marín-Blázquez, Gregorio Martínez Pérez, Francisco Esquembre – UMU; Alberto Huertas Celdrán – University of Zürich.
A Security and Trust Framework for Decentralized 5G Marketplaces
- Abstract: Billions of IoT devices lacking proper security mechanisms have been manufactured and deployed for the last years, and more will come with the development of Beyond 5G technologies. Their vulnerability to malware has motivated the need for efficient techniques to detect infected IoT devices inside networks. With data privacy and integrity becoming a major concern in recent years, increasing with the arrival of 5G and Beyond networks, new technologies such as federated learning and blockchain emerged. They allow training
machine learning models with decentralized data while preserving its privacy by design. This work investigates the possibilities enabled by federated learning concerning IoT malware detection and studies security issues inherent to this new learning paradigm. In this context, a framework that uses federated learning to detect malware affecting IoT devices is presented. N-BaIoT, a dataset modeling network traffic of several real IoT devices while affected by malware, has been used to evaluate the proposed framework.
As an additional contribution and to measure the robustness of the federated approach, an adversarial setup with several malicious participants poisoning the federated model has been considered. The baseline model aggregation averaging step used in most federated learning algorithms appears highly vulnerable to different attacks, even with a single adversary. The performance of other model aggregation functions acting as countermeasures is thus evaluated under the same attack scenarios. These functions provide a significant improvement against malicious participants, but more efforts are still needed to make federated approaches robust.
- Related Info: paper can be read here
- Authors: Jose María Jorquera Valero, Manuel Gil Perez, and Gregorio Martínez Perez – UMU
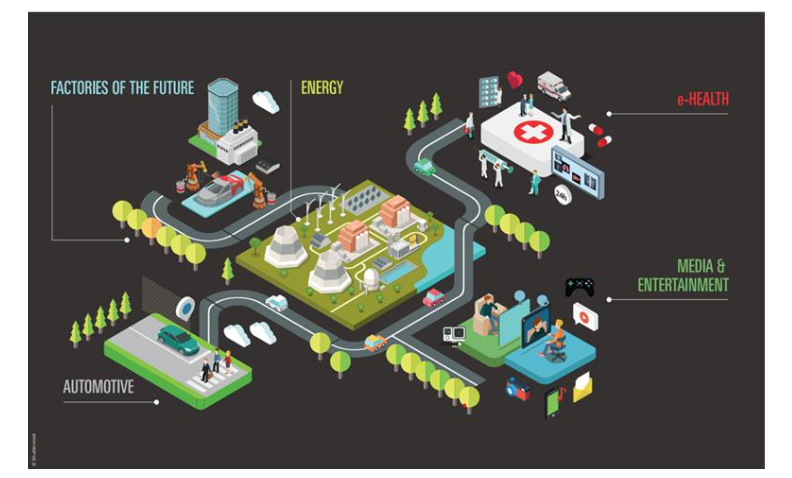
Empowering Vertical Industries through 5G Networks Current Status and Future Trends
- Abstract: This white paper summarizes the progress and key findings produced by 5G PPP projects to provide 5G network services for vertical industries. It provides information about requirements and business cases addressed by the projects. It discusses in detail several exemplary use cases from 11 different vertical sectors and identifies key 5G features that have been used to meet the specified requirements.
- Related Info: paper can be read here
- Authors: Giada Landi, Gino Carrozzo, Nicola Ciulli – Nextworks; Pouria Khodashenas – i2CAT; Roberto Riggio – FBK;
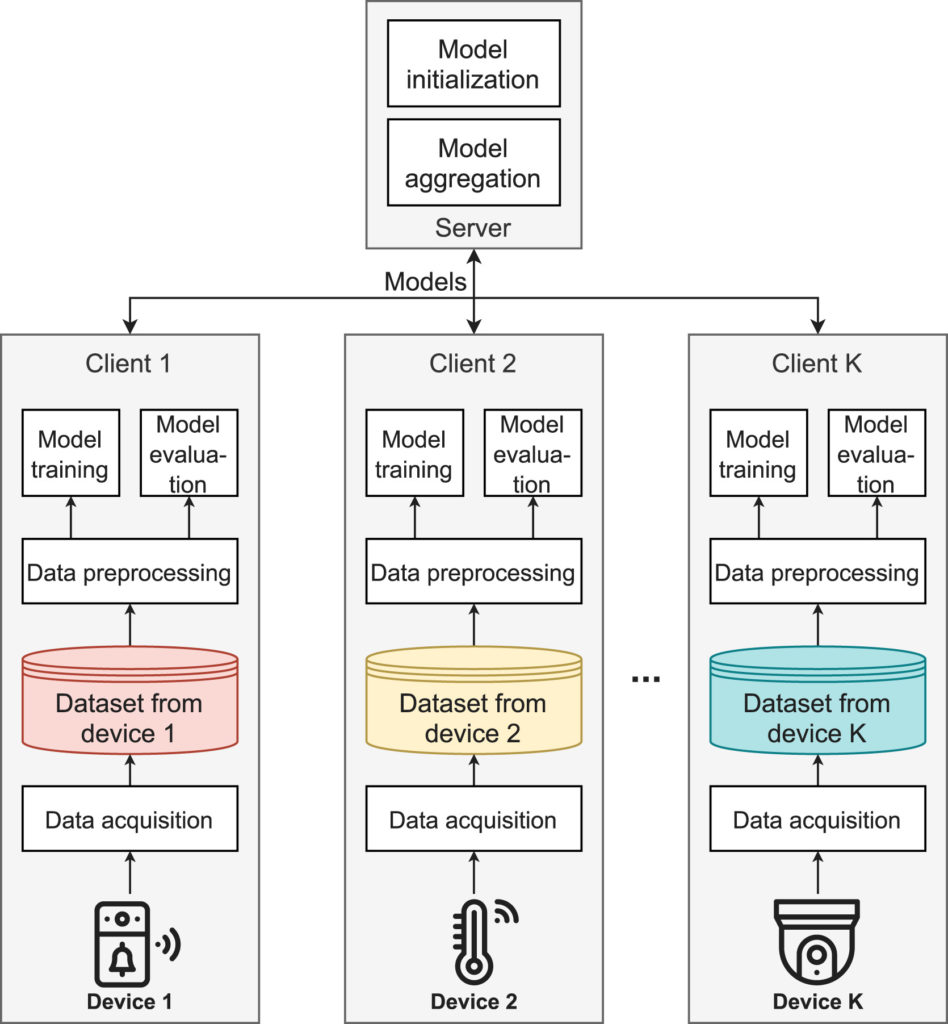
Federated learning for malware detection in IoT devices
- Abstract: Billions of IoT devices lacking proper security mechanisms have been manufactured and deployed for the last years, and more will come with the development of Beyond 5G technologies. Their vulnerability to malware has motivated the need for efficient techniques to detect infected IoT devices inside networks. With data privacy and integrity becoming a major concern in recent years, increasing with the arrival of 5G and Beyond networks, new technologies such as federated learning and blockchain emerged. They allow training
machine learning models with decentralized data while preserving its privacy by design. This work investigates the possibilities enabled by federated learning concerning IoT malware detection and studies security issues inherent to this new learning paradigm. In this context, a framework that uses federated learning to detect malware affecting IoT devices is presented. N-BaIoT, a dataset modeling network traffic of several real IoT devices while affected by malware, has been used to evaluate the proposed framework.
As an additional contribution and to measure the robustness of the federated approach, an adversarial setup with several malicious participants poisoning the federated model has been considered. The baseline model aggregation averaging step used in most federated learning algorithms appears highly vulnerable to different attacks, even with a single adversary. The performance of other model aggregation functions acting as countermeasures is thus evaluated under the same attack scenarios. These functions provide a significant improvement against malicious participants, but more efforts are still needed to make federated approaches robust.
- Related Info: paper can be read here
- Authors:from 5GZORRO, Pedro Miguel Sánchez Sánchez, Universidad de Murcia
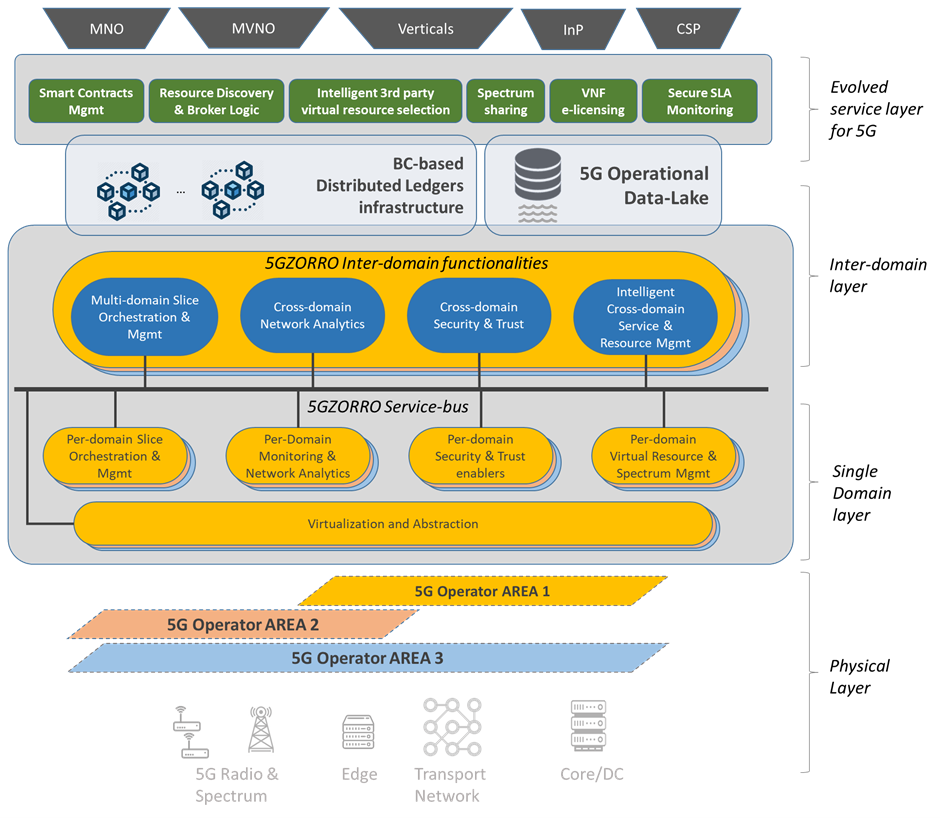
Dynamic Slice Scaling Mechanisms for 5G Multi-domain Environments
- Abstract: Network slicing is an essential 5G innovation whereby the network is partitioned into logical segments, so that Communication Service Providers (CSPs) can offer differentiated services for verticals and use cases. In many 5G use cases, network requirements vary over time and CSPs must dynamically adapt network slices to satisfy the contractual network slice QoS, cooperating, and using each other’s resources, e.g., when resources of a single CSP are not sufficient or suitable to maintain all its current SLAs. While this need for dynamic cross-CSP cooperation is widely recognized, realization of this need is not yet possible due to gaps both in business processes and in technical capabilities.
In this paper, we present a 5GZORRO approach to dynamic cross-CSP slice scaling. Our approach both enables CSPs to collaborate, providing security, and trust with smart multi-party contracts, and facilitates thus achieved collaboration to enable resource sharing across multiple administrative domains, either during slice establishment or when already existing slice needs to expand or shrink. Our approach allows automating both business and technical processes involved in dynamic lifecycle management of cross-CSP network slices, following ETSI’s Zero-Touch Network and Service Management (ZSM) closed-loop architecture, and relying on resource-sharing Marketplace, Distributed Ledger (DL), and Operational Data Lake. We show how this approach is realized in truly Cloud Naive way, with Kubernetes as both business and technical cross-domain orchestrator. We then showcase applicability of the proposed solution for dynamic scaling of Content Delivery Network (CDN) service.
This paper was published in: IEEE 7th International Conference on Network Softwarization (NetSoft) (28 June-2 July 2021)
Date Added to IEEE Xplore: 26 July 2021
DOI: 10.1109/NetSoft51509.2021.9492716
- Related Info: paper can be read here
- Authors: David Breitgand, Avi Weit, Katherine Barabash, IBM Israel; Alexios Lekidis, Vasileios Theodorou, Intracom Telecom; Rasoul Behravesh, Cristina E. Costa, FBK; Pietro Giardina, Nextworks
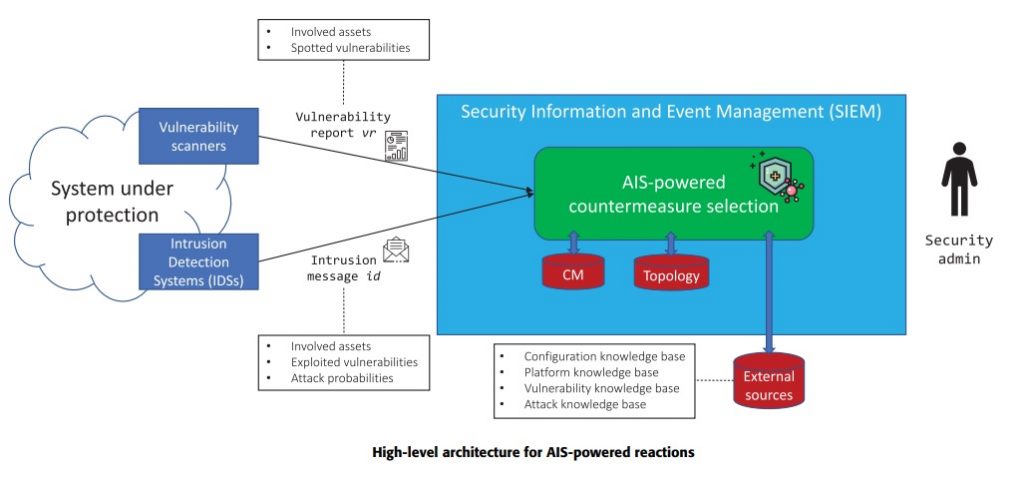
AISGA: Multi-Objective Parameters optimization for Countermeasures Selection through Genetic Algorithm
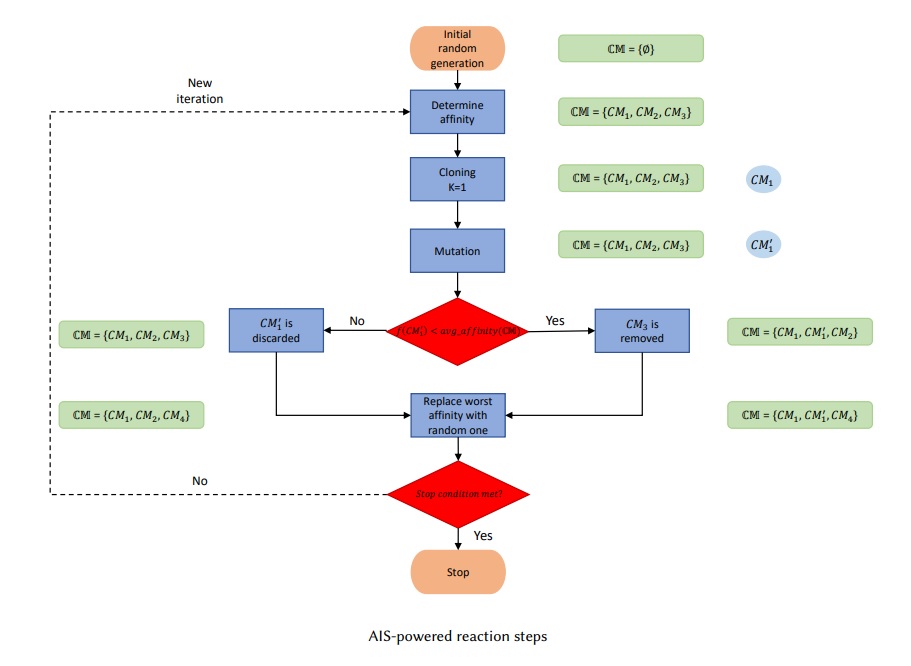
- Abstract: Cyberattacks targeting modern network infrastructures are increasing in number and impact. This growing phenomenon emphasizes the central role of cybersecurity and the reaction against ongoing threats targeting assets within the protected system. The Artificial Immune System (AIS) methodology is able to calculate the optimal set of atomic countermeasures to enforce on the asset within the monitored system, minimizing the risk to which those are exposed in a more than adequate time. Moreover, this paper presents AISGA, a multi-objective approach that leverages the capabilities of a Genetic Algorithm (GA) to optimize the selection of the input parameters of the AIS methodology. Among others, acknowledge of this work was partially supported by the University of Murcia and the European Commission through 5GZORRO.
- Related Info: paper can be read here
- Authors: Pantaleone Nespoli, Félix Gómez Mármol, Georgios Kambourakis – Universidad de Murcia
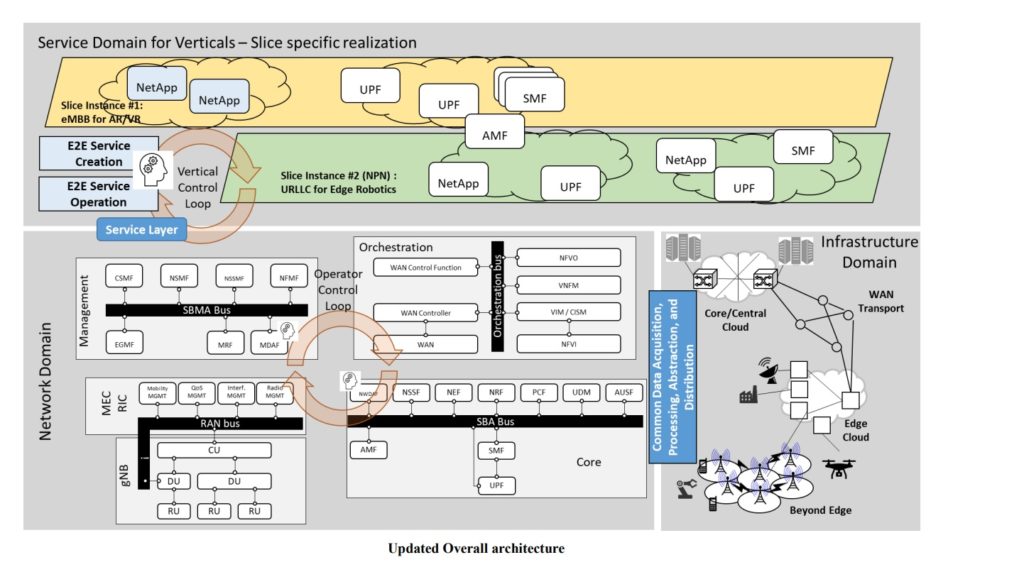
5G PPP Architecture Working Group - View on 5G Architecture, Version 4.0
- Abstract: The overall goal of the Architecture Working Group (WG) within the 5G PPP Initiative is to consolidate the main technology enablers and the bleeding-edge design trends in the context of the 5G Architecture. This current version 4 of the white paper is focusing on the output of the Phase III projects, discussing the latest findings in terms of the integration of large infrastructure and vertical industries, the long-term evolution of the 5G technologies, and the service-specific features. It provides a consolidated view of the architectural efforts developed in the projects part of the 5G PPP initiative and other research efforts, including standardization. This effort serves not only to review the current state of the art, but also to identify promising trends towards the next generation of mobile and wireless communication networks, namely, 6G.
Regarding 5GZORRO, the ability to trade 5G resources (including radio and spectrum ones) across different domains enlarges the set of network resources and extends it to abstractions like services and slices, opening the door to a richer 5G business ecosystem. The 5GZORRO Marketplace leverages the use of DLT and Smart Contracts technologies to enable the trade of 5G resources.
- Related Info: paper can be read here
- Authors:Giada Landi, Francesca Moscatelli, Nextworks; Katherine Barabash, IBM; Diego R. López, Jose Ordonez-Lucena, David Artuñedo, Telefónica; Borja Otura García, ATOS; Miguel Catalán, i2CAT.
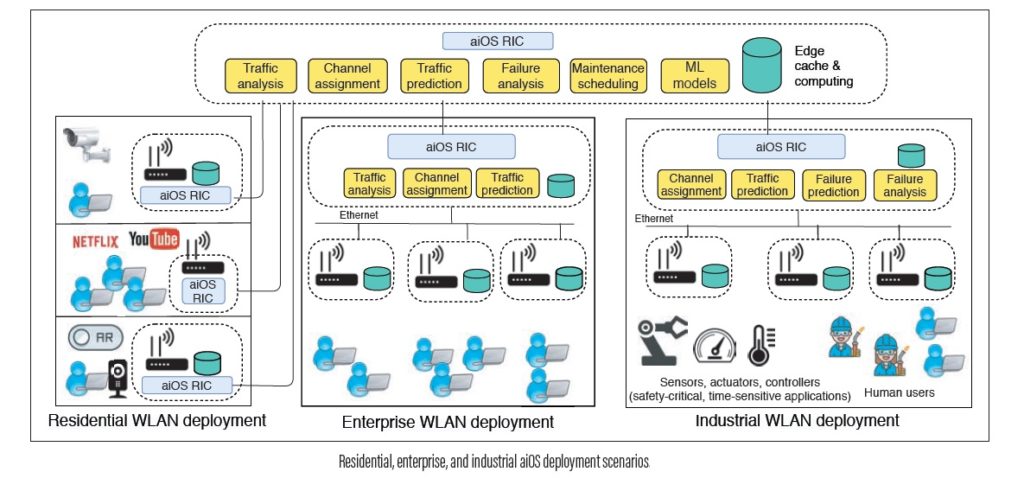
AI Empowered Software Defined WLANs
- Abstract: The complexity of wireless and mobile networks is growing at an unprecedented pace. This trend is proving current network control and management techniques based on analytical models and simulations to be impractical, especially if combined with the data deluge expected from future applications such as augmented reality. This is particularly true for software-defined wireless local area networks (SD-WLANs). To battle this growing complexity, future SD-WLANs must follow an artificial intelligence (AI) -native approach. In this article, we introduce aiOS, which is an AI-based platform that builds toward the autonomous management of SD-WLANs. Our proposal is aligned with the most recent trends in in-network AI promoted by the ITU Telecommunication Standardization Sector (ITU-T) and with the architecture for disaggregated radio access networks promoted by the Open Radio Access Network Alliance. This work has been performed in the framework of the European Union’s Horizon 2020 project 5GZORRO. This work was published on IEEE Communications Magazine on March 2021.
- Related Info: paper can be read here
- Authors: Estefania Coronado – i2CAT; Abin Thomas – FBK; Suzan Bayhan – University of Twente; Roberto Riggio -RISE.
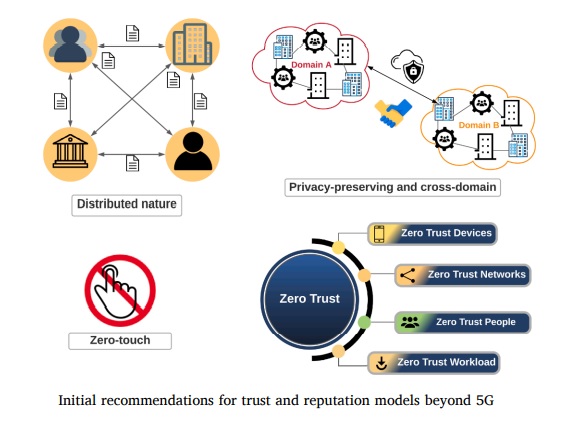
Toward pre-standardization of reputation-based trust models beyond 5G
Article published on the Journal Elsevier – Computer Standards & Interfaces – volume 81 April 2022
- Abstract: In the last years, the number of connections in mobile telecommunication networks has increased rampantly; so, the number and type of relationships among entities. Such interactions need to be profitable since entities will need to rely on each other. Mobile telecommunication networks demand trust and reputation models that allow developing feasible communications in 5G and beyond networks, through which a group of entities can establish chains of services between cross-operators/domains, with security and trust worthiness. One of the key obstacles to achieving generalized connectivity beyond 5G networks is the lack of automatized, efficient, and scalable models for establishing security and trust. This article proposes a pre-standardization approach for reputation-based trust models beyond 5G. To this end, we have realized a thorough review of the literature to match trust standardization approaches. An abstract set of requirements and key performance indicators has been extracted, and some pre-standardization recommendations proposed to fulfill essential conditions of future networks and to cover the lack of common trust and reputation models beyond 5G.
- Related Info: paper can be read here
- Authors: José María Jorquera Valero, Pedro Miguel Sánchez Sánchez, Manuel Gil Pérez, Alberto Huertas Celdrán, Gregorio Martínez Pérez – Universidad de Murcia.
Time-Sensitive Mobile User Association and SFC Placement in MEC-Enabled 5G Networks
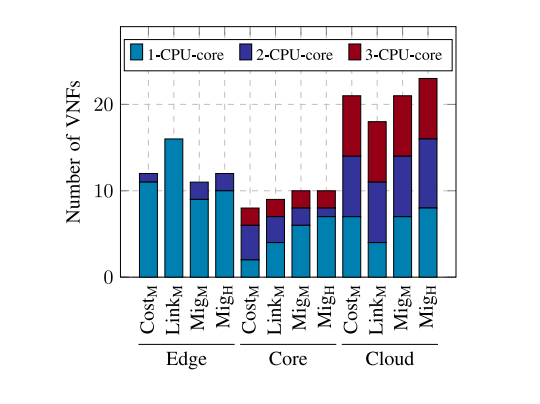
- Abstract: The ongoing roll-out of 5G networks paves the way
for many fascinating applications such as virtual reality (VR),
augmented reality (AR), and autonomous driving. Moreover, 5G
enables billions of devices to transfer an unprecedented amount
of data at the same time. This transformation calls for novel
technologies like multi-access edge computing (MEC) to satisfy
the stringent latency and bitrate requirements of the mentioned
applications. The main challenge pertaining to MEC is that the
edge MEC nodes are usually characterized by scarce computational resources compared to the core or cloud, arising the
challenge of efficiently utilizing the edge resources while ensuring that the service requirements are satisfied. When considered
with the users’ mobility, this poses another challenge, which
lies in minimization of the service interruption for the users
whose service requests are represented as service function chains
(SFCs) composed of virtualized network functions (VNFs) instantiated on the MEC nodes or on the cloud. In this paper, we study the problem of joint user association, SFC placement,
and resource allocation, employing mixed-integer linear programming (MILP) techniques. - Related Info: paper can be read here
- Authors: Rasoul Behravesh , Davit Harutyunyan , Estefanía Coronado , Member, IEEE and Roberto Riggio , Senior Member, IEEE
A Bio-Inspired Reaction Against Cyberattacks: AIS-Powered Optimal Countermeasures Selection
- Abstract: Nowadays, Information and Communication Technology (ICT) infrastructures play a crucial role for human beings, providing essential services at astonishing speed.Nevertheless, such a centrality of those infrastructures attracts the interest of ill-motivated actors that target such infrastructures with cyberattacks that are every day more sophisticated and more disruptive. In this alarming context, selecting the optimal set of countermeasures represents a primary need to react against the appearance of potentially dangerous threats effectively. With the motivation to contribute to developing faster and more effective response capabilities against them, the paper at hand introduces a novel cybersecurity reaction methodology based on Artificial Immune Systems (AIS), for which the evolutionary computing paradigm has been adopted. By leveraging the outstanding properties of these bio-inspired techniques, the selected countermeasures to defeat cyberthreats through cloning and mutation phases to improve the quality of the solution from a quantitative perspective, being able to adjust the risk to which the assets of the protected system are exposed. Exhaustive experiments demonstrate the feasibility of the proposed approach, reducing the risk in a more than acceptable time lapse. This work was supported in part by 5GZORRO.
- Related Info: paper can be read here
- Authors:Pantaleone Nespoli, Félix Gómez Mármol – Universidad de Murcia; Jorge Maestre Vidal – Digital Lab.
Trusted Execution Environment-enabled platform for 5G security and privacy enhancement
- Abstract:With the deployment of 5G networks and the beginning of the design of beyond 5G communications, new critical requirements are emerging in terms of performance, security, and trust for leveraged technologies, such as Software Defined Networking (SDN) and Network Function Virtualization (NFV). One of the requirements at the security and trust level is that when delegating critical tasks and data to the infrastructure deployed in an external domain, the client needs guarantees that the execution has been carried out securely, without data breaches or compromises during computing tasks. for useful insights to this work from 5GZORRO Consortium.
- Related Info: paper can be read here
- Authors: José María Jorquera Valero, Pedro Miguel Sánchez Sánchez, Manuel Gil Pérez, Alberto Huertas Celdrán, Gregorio Martínez Pérez – Universidad de Murcia
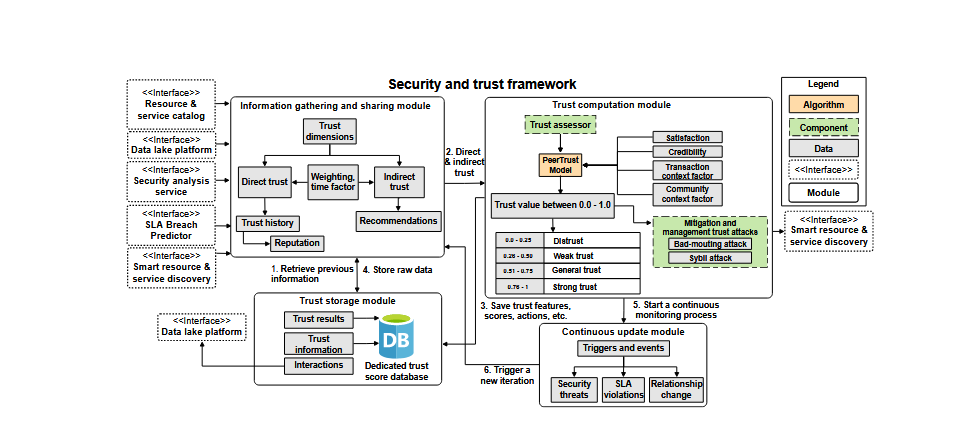
Design of a Security and Trust Framework for 5G Multi‑domain Scenarios
- Abstract: A 5GZORRO Article published in the prestigious Journal of Network and Systems Management (#JNSM) Springer – Volume 30, issue 1, January 2022: ‘Design of a security and trust framework for 5G multi-domain scenarios’ In 5G-enabled scenarios, adversaries can exploit vulnerabilities associated with resource sharing to perform lateral movements targeting other tenant resources, as well as to disturb the 5G services ofered or even the infrastructure resources. Moreover, existing security and trust models are not adequate to react to the dynamicity of the 5G infrastructure threats nor to the multi-tenancy security risks.5GZORRO proposes in this work a new security and trust framework for 5G multi-domain scenarios. To motivate its application, we detail a threat model covering multi-tenant scenarios in an underlying 5G network infrastructure. We also propose diferent ways to mitigate these threats by increasing the security and trust levels using network security monitoring, threat investigation, and end-to-end trust establishments.The framework is applied in a realistic use case of 5GZORRO- H2020 project, which envisions a multi-tenant environment where domain owners share resources at will.
- Related Info: paper can be read here
- Authors: José María Jorquera Valero, Pedro Miguel Sánchez Sánchez, Manuel Gil Pérez, Alberto Huertas Celdrán, Gregorio Martínez Pérez – Universidad de Murcia; Javier Fernandez Hidalgo, M. Shuaib Siddiqui – i2CAT; Alexios Lekidis – Intracom-Telecom
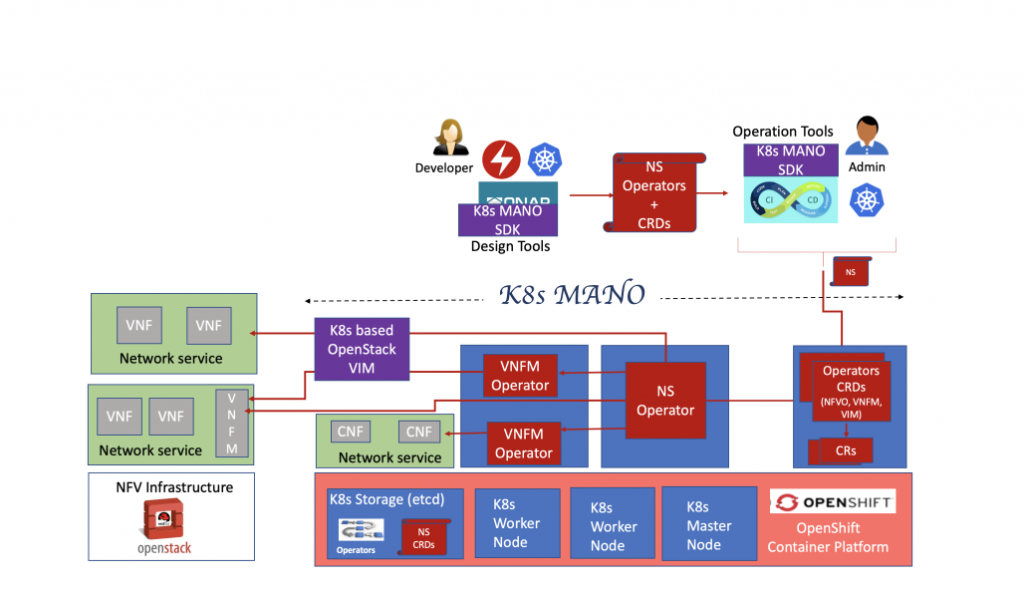
Toward True Cloud Native NFV MANO
- Abstract: The telecommunication industry is making a major
shift towards cloud native Network Functions Virtualization.
However, being cloud native implies more than just replacing
Virtual Machines with containers. The cloud native approach changes the way virtual network functions are being composed, deployed, and configured as network services and how these services are being orchestrated and managed at run time. Traditional Network Management and Orchestration (MANO) frameworks
are implemented via specialized engines that have been conceived
prior to the cloud native era. Thus, they inherit many traits, which impede pivoting to cloud native. In this paper we focus on some fundamental challenges and propose a novel cloud native MANO architecture that exploits advantages of Kubernetes
- Related Info: paper can be read here
- Authors: David Breitgand, Vadim Eisenberg, Nir Naaman, Nir Rozenbaum, Avi Weit IBM Research – Haifa, Israel
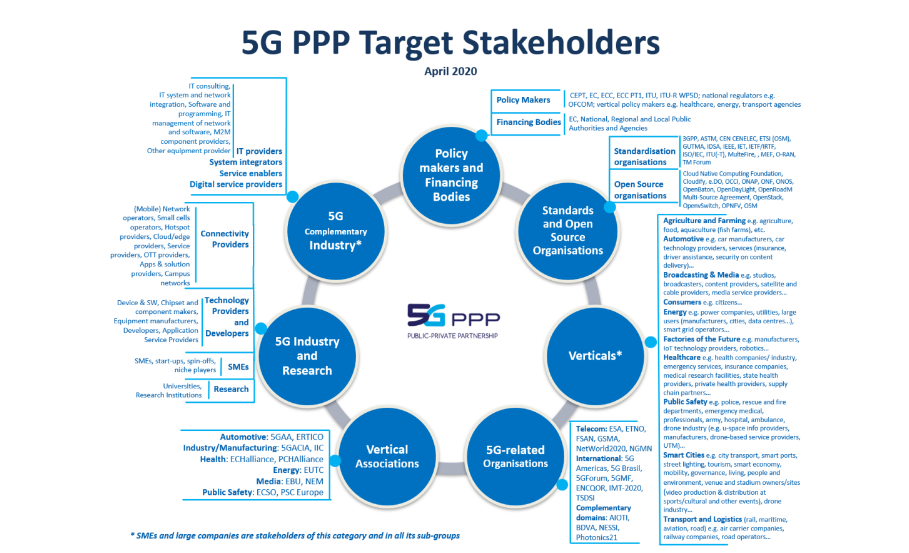
5G Ecosystems 2021
- Abstract:
Europe is investing significant resources in research and technology development of 5G networks through the 5G Private Public Partnership (5G PPP). In addition to various scientific and technological topics, the effort focuses on societal and business challenges creating value with 5G networks. This white paper discusses 5G ecosystems as a prerequisite for value creation for and by the engaged stakeholders and return of investment as a potential award for the engagement.
A clear identification of 5G stakeholders supports the creation and evolution of the 5G ecosystems by characterising the potential role that each actor can assume. The identified stakeholder groups include 5G industry and research organisations, vertical sectors’ firms, complementor firms, as well as organisations and associations of providers and consumers active in the value network representing the interests of a larger collection of firms and organisations. Those stakeholder groups include both small and medium enterprises (SME) and larger companies, and whenever relevant academic institutions. In addition, standards organisations, open-source organisation and policy makers are an inherent part of the 5G ecosystems, as are governmental agencies at regional, national and European level that support the creation of value in the 5G ecosystems though funding or procurement of innovations.
Related Info: paper can be read here
Authors: Sergi Figuerola, Eunice Ribeiro – i2CAT
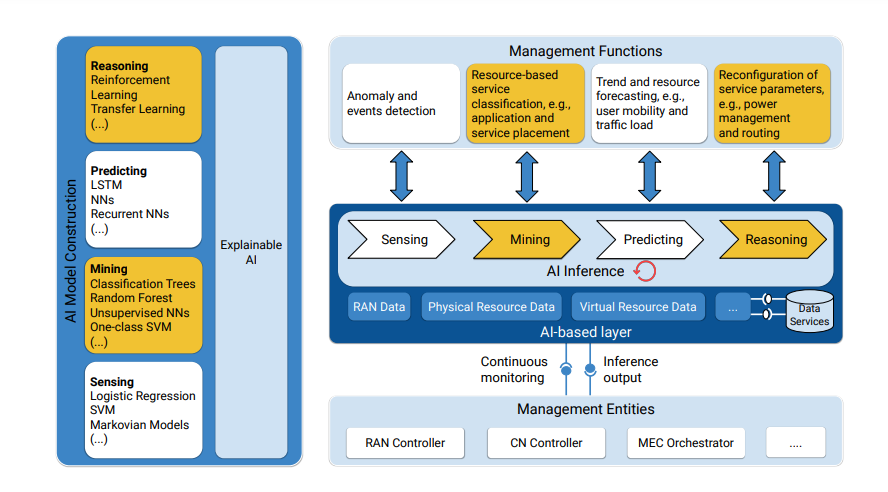
AI and ML –Enablers for Beyond 5G Networks
- Abstract: 5GZORRO has contributed to this white paper on AI/ML as enablers of 5G and B5G networks. The white paper is based on contributions from 5G PPP projects that research, implement and validate 5G and B5G network systems. The white paper discusses the application of AI/ML in the 5G network architecture. In this context is identifies solutions pertaining to AI-based autonomous slice management, control and orchestration, AI/ML-based scaling operations in network service orchestration, AI/ML as a Service in network management and orchestration, enablement of ML for the verticals’ domain, cross-layer optimization, management analytics in general, 3rd party ML analytics for network operation optimization in particular, anomaly detection using AI/ML. In the context of architecture it discusses the requirements for ML model lifecycle and interface management. Furthermore it investigates the global efforts for the enablement of AI/ML in networks, including the network data analytics function, the lack of availability of data-sets for training the AI/ML models and the associated privacy concerns. Finally, it identifies the challenges in view of trust in AI/ML-based networks and potential solutions such as the zero-trust management approach. The section concludes with a brief overview of AI/ML-based KPI validation and system troubleshooting.
- Related Info: paper can be read here
- Authors: Alexios Lekidis (ICOM) Rasoul Behravesh (FBK), Tejas Subramanya (FBK), Pedro Miguel Sánchez Sánchez (UMU), José María Jorquera Valero (UMU), Alberto Huertas Celdrán (UMU), Manuel Gil Pérez (UMU), Gregorio Martínez Pérez (UMU), Gino Carrozzo (NXW)
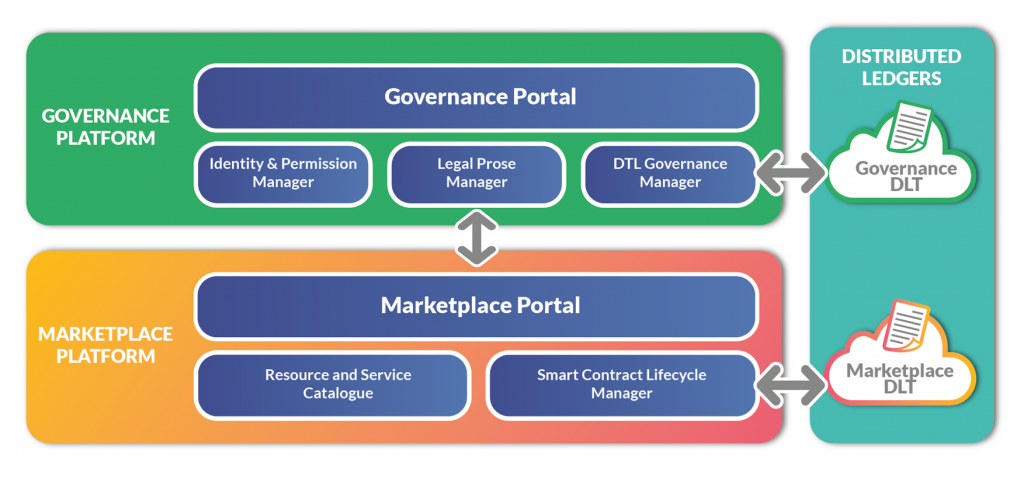
Multi-Party Collaboration in 5G Networks via DLT-Enabled Marketplaces: A Pragmatic Approach
- Abstract: To fully cope with the requirements of innovative 5G use cases, evolving business models and flexible networking scenarios spanning multiple administrative domains are envisioned. In this context, transparent and trusted frameworks that enable network service providers and infrastructure providers to advertise, negotiate, and acquire, in real-time, 5G resources and services, distributed over various geographical areas, are extremely valuable. To address this goal, emerging Distributed Ledger Technologies (DLTs) arise as well-suited solutions to ensure distributed security and trust, as well as effective and agile transaction management across the various parties involved in the 5G service chain implementation. Following this vision, this paper presents the design of a DLT-enabled Marketplace aimed to foster the secure trading of heterogeneous resources in dynamic 5G ecosystems.
- Related Info: paper can be read here
- Authors: Fundació i2CAT, Spain; Nextworks, Italy; BARTR Group, UK; Altice Labs, Portugal; University of Murcia, Spain; Telefonica, Spain.
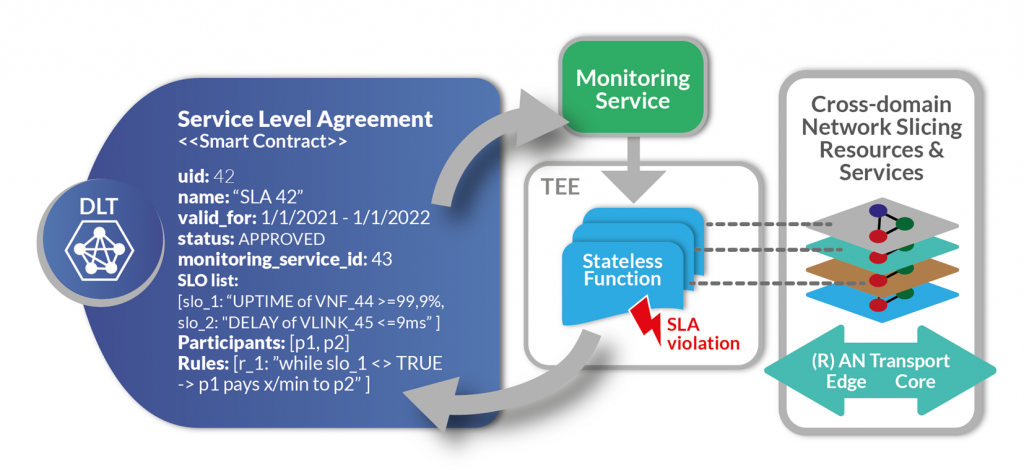
Blockchain-Based Zero Touch Service Assurance in Cross-Domain Network Slicing
- Abstract: 5G infrastructure can be optimised through the inclusion of resource sharing schemes within Network Function Virtualisation (NFV) ecosystems and extended capabilities of network slicing services (reducing the costs for operators to scale up their network coverage). In such environments, marketplaces are formed to facilitate the exchange of NFV services across administrative domains, which may, however, belong to untrusted and unreliable entities. In this work, we propose a novel zero-touch approach for cross-domain network slicing service assurance, using enterprise blockchain technologies and employing an AI-driven closed-loop automation architecture. Our approach is based on the lifecycle management of Service Level Agreements (SLAs) using smart contracts – from service negotiation to service binding, monitoring, reconfiguration, and decommissioning.
- Related Info: paper can be read here
- Authors: Intracom Telecom, Greece; IBM I, Israel; Fundació i2CAT, Spain; Ubiwhere, Portugal; Fondazione Bruno Kessler, Italy; BARTR, UK.
Zero-Touch AIOps in Multi-Operator 5G Networks
- Abstract: Automation and intelligence are key functionalities for implementing smart network management decisions in 5G/6G softwarised networks. In this work, we present the 5GZORRO approach for applying Artificial Intelligence to network operations (AIOps). The goal of the 5GZORRO AIOps is to implement truly zero-touch automation of operation and maintenance tasks in the specific context of multi-operator networks. The approach goes beyond the current state of the art of single domain 5G networks and paves the way to an evolution of Network management from 5G towards 6G. In this paper, we shortly cover the motivation, explain the technology, and show how heavily it relies on secure, reliable, and intelligent data collection, aggregation and processing. We put forward our assessment of domain specific requirements and challenges and introduce 5GZORRO Operational Data Lake, one of the major innovations towards fully automated multi-operator networks required for smooth progression into 6G.
- Related Info: paper can be read here
- Authors:Katherine Barabash, Dean Lorenz, and Kalman Meth (IBM Israel), Gino Carrozzo (Nextworks Italy), Shuaib M. Siddiqui (I2CAT Spain)
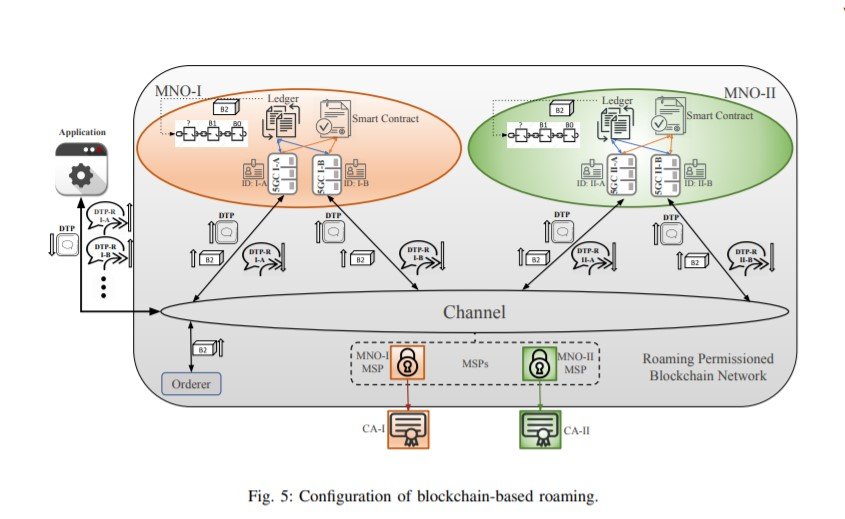
Smart Contracts in the 5G Roaming Architecture: The Fusion of Blockchain with 5G Networks
- Abstract: The roll-out of the fifth generation of cellular network (5G) technology has generated a new surge of interest in the potential of blockchain to automate various use cases involving cellular networks. 5G is indeed expected to offer new market opportunities for small and large enterprises alike. In this article, we introduce a new roaming network architecture for 5G based on a permissioned blockchain platform with smart contracts. The proposed solution improves the visibility for mobile network operators of their subscribers’ activities in the visited network, as well as enabling quick payment reconciliation and reducing fraudulent transactions. The paper further reports on the methodology and architecture of the proposed blockchain-based roaming solution using the Hyperledger platform.This work has been performed within the EU’s H2020 projects 5G-CARMEN (825012), and 5G-ZORRO (871533) and funded through a collaborative program between the University of Bologna and the Fondazione Bruno Kessler.
- Related Info: paper can be read here
- Authors: Babak Mafakheri, University of Bologna, Fondazione Bruno Kessler; Andreas Heider-Aviet, Deutsche Telekom 5G Program; Roberto Riggio, RISE Research Institutes of Sweden AB (former I2CAT); Leonardo Goratti, Safran Passenger Innovations GmbH.
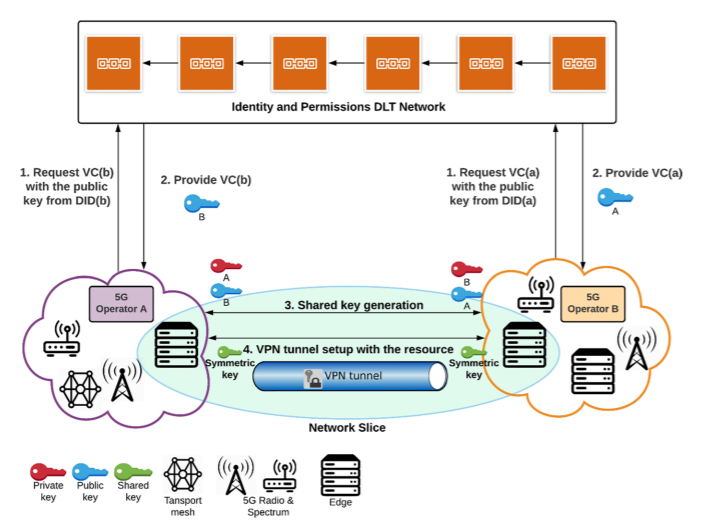
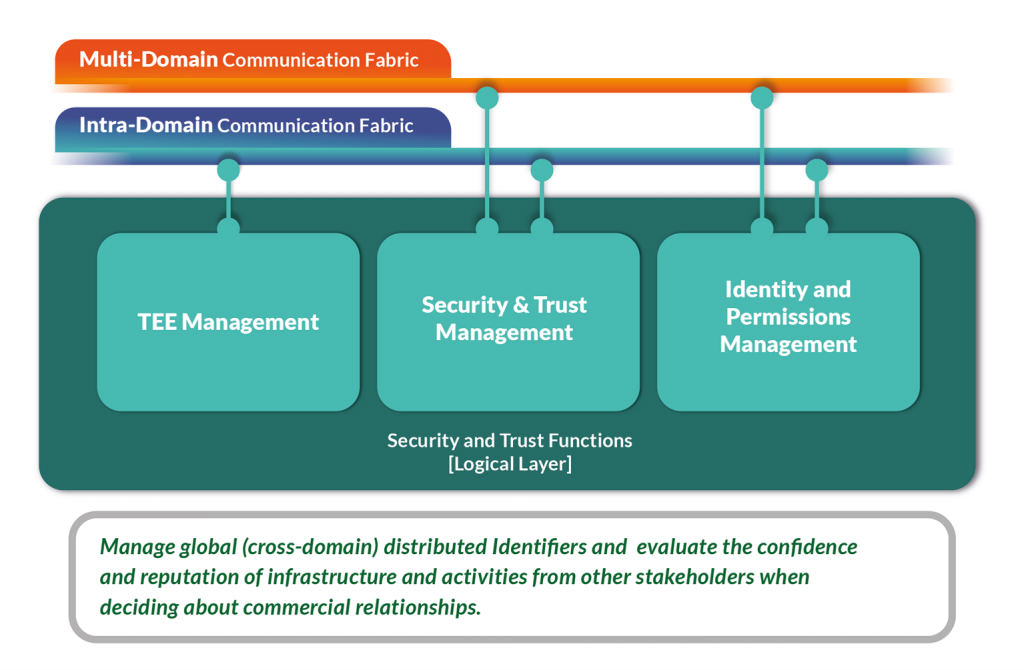
Overview of the Security and Trust Mechanisms in the 5GZORRO Project
- Abstract: Thee H2020 5GZORRO project proposes new security and trust solutions for multi-domain and multi-stakeholder scenarios in 5G and beyond networks. To deal with the utmost importance security and trust challenges, we introduce different modules to mitigate them, namely, integrity and non-repudiation through Distributed Ledger Technologies, decentralized identity through an Identity and Permission Manager, end-to-end trustworthy relationships via a Trust ManagementFramework, secure workloads across different tenants and stakeholders via Trusted Execution Environment Security Management, detection and response to internal vulnerabilities and attacks via Network Monitoring, and on-demand secure cross-domain connections via VPN-as-a-Service. Therefore, the built security and trust 5GZORRO mechanisms form a secure environment with zero-touch automation capabilities, minimizing human interventionIn the evolution from 5G to beyond 5G networks, new business models are emerging where multi-domain and multistakeholder scenarios will play a paramount role as enablers.
- Related Info: paper can be read here
- Authors: José M. Jorquera Valero and Pedro Miguel Sánchez Sánchez (University of Murcia, Spain); Alexios Lekidis (Intracom Telecom, Greece); James Taylor (Bartr Group, United Kingdom (Great Britain)); Javier Fernandez Hidalgo and Adriana Fernández-Fernández (Fundació i2CAT, Internet i Innovació Digital a Catalunya, Spain); Paulo Chainho and Bruno Santos (Altice Labs, Portugal); Jean-Marie Mifsud and Antoine Sciberras (Malta Communications Authority, Malta); Muhammad Shuaib Siddiqui (Fundació i2CAT, Internet i Innovació Digital a Catalunya, Spain); Manuel Gil Pérez, Alberto Huertas Celdrán and Gregorio Martinez Perez (University of Murcia, Spain)
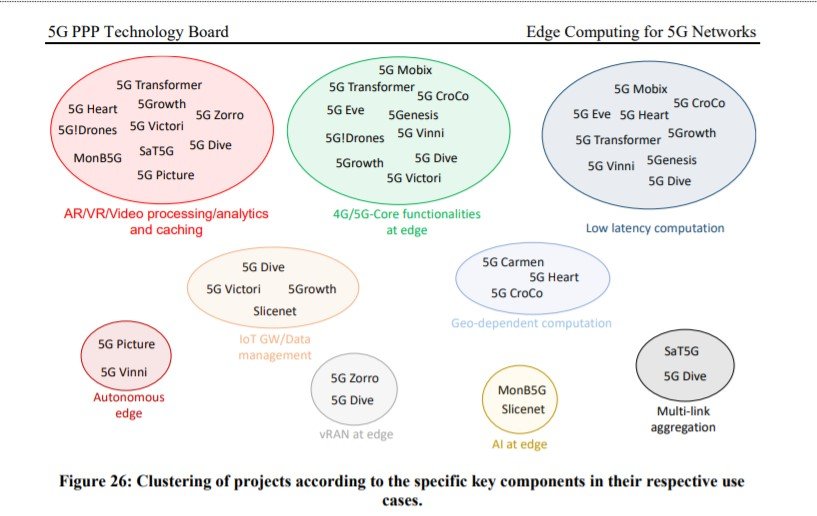
Edge Computing for 5G Networks
- Abstract: This whitepaper presents a rationale on why and how 5G can benefit from Edge Computing; a review on how 5GPPP projects have been using and enhancing Edge Computing for 5G and beyond systems. The 5G PPP Initiative and the 5GIA are happy to present a new white paper entitled “Edge Computing for 5G Networks”. This white paper provides a) a brief introduction to the Edge computing concept, b) an exhaustive technology review focusing on virtualisation, orchestration, network control, and operational frameworks, c) a discussion about the role of security, and d) an analysis of several business aspects around the Edge ecosystem. Moreover, the white paper provides an in-depth analysis of Edge solutions that have been selected, deployed and validated by 17 different EU funded 5G PPP projects. Read the 5GZORRO contribution.
- Related Info: paper can be read here
- Authors: David Breitgand (IBM), Gino Carrozzo(NXW)
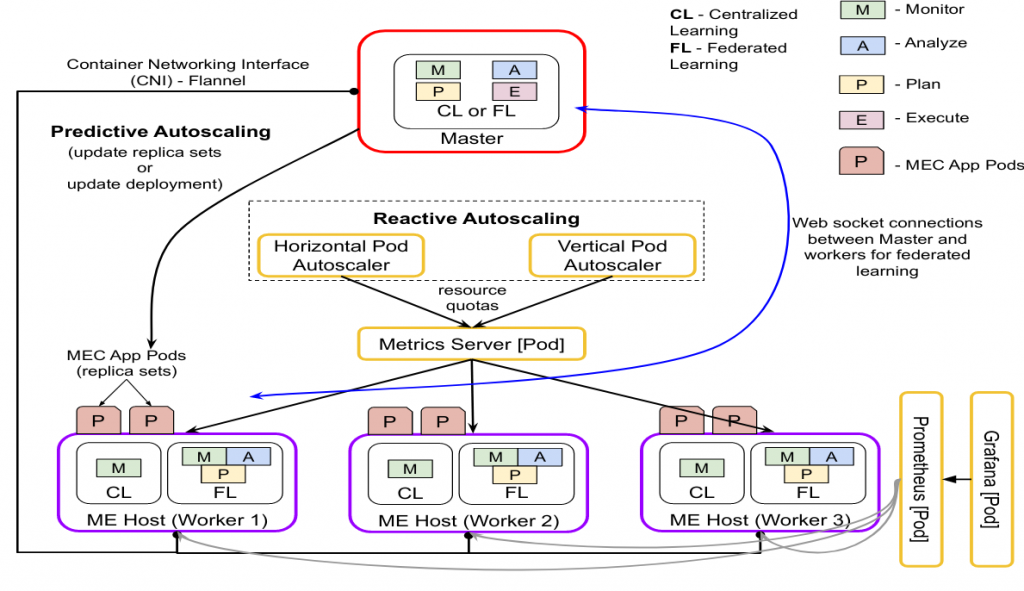
Centralized and Federated Learning for Predictive VNF Autoscaling in Multi-domain 5G Networks and Beyond
- Abstract: Network Function Virtualization (NFV) and Multi-access Edge Computing (MEC) are two technologies expected to play a vital role in 5G and beyond networks. However, adequate mechanisms are required to meet the dynamically changing network service demands to utilize the network resources optimally and also to satisfy the demanding QoS requirements. Particularly in multi-domain scenarios, the additional challenge of isolation and data privacy among domains needs to be tackled. To this end, centralized and distributed Artificial Intelligence (AI)-driven resource orchestration techniques (e.g., virtual network function (VNF) autoscaling) are foreseen as the main enabler. In this work, we propose deep learning models, both centralized and federated approaches, that can perform horizontal and vertical autoscaling in multi-domain networks.
- Related Info: paper can be read here
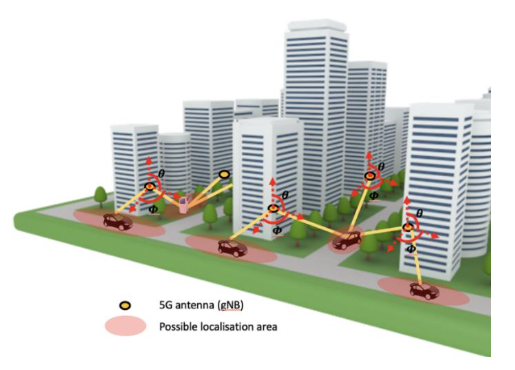
AI-driven Zero-touch Operations, Security and Trust in Multi-operator 5G Networks: a Conceptual Architecture
- Abstract: The 5G network solutions currently standardised and deployed do not yet enable the full potential of pervasive networking and computing envisioned in 5G initial visions: network services and slices with different QoS profiles do not span multiple operators; security, trust and automation is limited. The evolution of 5G towards a truly production-level stage needs to heavily rely on automated end-to-end network operations, use of distributed Artificial Intelligence (AI) for cognitive network orchestration and management and minimal manual interventions (zero-touch automation). All these elements are key to implement highly pervasive network infrastructures. Moreover, Distributed Ledger Technologies (DLT) can be adopted to implement distributed security and trust through Smart Contracts among multiple non-trusted parties. In this paper, we propose an initial concept of a zero-touch security and trust architecture for ubiquitous computing and connectivity in 5G networks. Our architecture aims at cross-domain security & trust orchestration mechanisms by coupling DLTs with AI-driven operations and service lifecycle automation in multi-tenant and multi-stakeholder environments. Three representative use cases are identified through which we will validate the work which will be validated in the test facilities at 5GBarcelona and 5TONIC/Madrid.
- Related Info: 5GZORRO paper can be read here
- Authors: Gino Carrozzo (Nextworks); M. Shuaib Siddiqui (I2CAT); August Betzler (I2CAT); José Bonnet (Altice Labs); Gregorio Martinez Perez (Univ. Murcia); Aurora Ramos (ATOS); Tejas Subramanya (Fondazione Bruno Kessler)
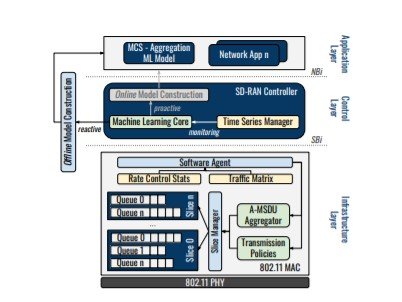
Adaptive ML-based Frame Length Optimisation in Enterprise SD-WLANs
- Abstract: Software-Defned Networking (SDN) is gaining a lot of traction in wireless systems with several practical implementations and numerous proposals being made. Despite instigating a shift from monolithic network architectures towards more modulated operations, automated network management requires the ability to extract, utilise and improve knowledge over time.Machine Learning (ML) is evolving from a simple tool applied in networking to an active component in what is known as Knowledge-Defned Networking (KDN). This work discusses the inclusion of ML techniques in the specifc case of Software-Defned Wireless Local Area Networks (SD-WLANs), paying particular attention to the frame length optimization problem.This work proposes an adaptive MLbased approach for frame size selection on a per-user basis by taking into account both specifc channel conditions and global performance indicators. The approach has been gauged by analysing a multitude of scenarios, with the results showing an average improvement of 18.36% in goodput over standard aggregation mechanisms.
- Related Info: paper can be read here
- Authors: Estefanía Coronado (Fondazione Bruno Kessler); Abin Thomas (FBK); Roberto Riggio (former FBK)
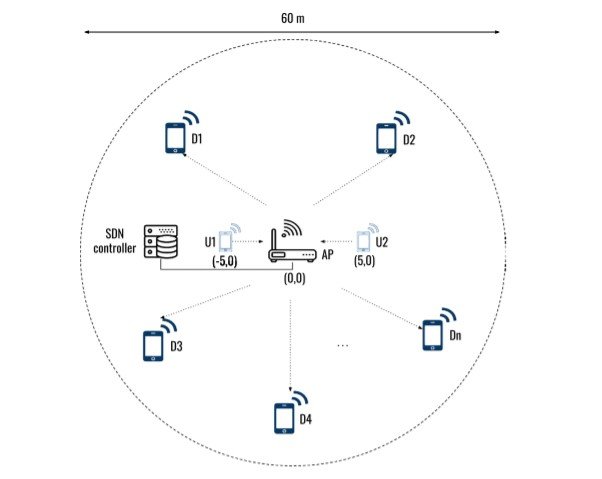
aiOS: An Intelligence Layer for SD-WLANs
- Abstract: Software-Defined Networking (SDN) promises to deliver a more manageable network whose behaviour could be easily changed using applications written in high-level declarative languages running on top of a logically centralized control plane resulting, on the one hand, in the mushrooming of complex point solutions to very specific problems and, on the other hand, in the creation of a multitude of network configuration options. This fact is especially true for 802.11-based Software-Defined WLANs (SD-WLANs). It is our standpoint that to tame this increase in complexity, future SD-WLANs must follow an Artificial Intelligence (AI) native approach.This paper presents aiOS, an AI-based Operating System for SD-WLANs. The aiOS is used to implement several Machine Learning (ML) models for user-adaptive frame length selection in SD-WLANs.An extensive performance evaluation carried out on a real-world testbed shows that this approach improves the aggregated network throughput by up to 55%. The entire implementation is released including the controller, the ML models, and the programmable data-path under a permissive license for academic use.
- Related Info: paper can be read here
- Authors: Estefanía Coronado (Fondazione Bruno Kessler); Abin Thomas (FBK); Suzan Bayhan (FKB); Roberto Riggio (former FBK)